Sponsored by Proofpoint
Sponsored by Proofpoint
How to Stop Social Media Hacks
Sponsored by Proofpoint
7 Steps to Reduce Social Account Takeover Risk
Sponsored by HelpSystems
2017 State of IBM i Security Study; Don't Leave Your Data Vulnerable
Sponsored by HelpSystems
When Malware Attacks Your IBM i, AIX, and Linux Servers; True Stories From the Field
Sponsored by HelpSystems
Best Practices for Audit & Compliance Reporting for Systems Running IBM i
Sponsored by HelpSystems
Close Security Gaps to Avoid a Data Breach
Sponsored by Lastline
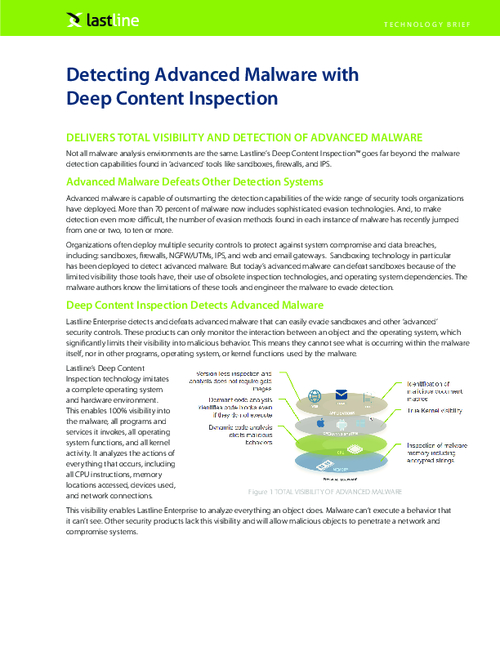
Detecting Advanced Malware with Deep Content Inspection
Sponsored by Lastline
Advanced Malware and How It Avoids Detection
Sponsored by Lastline
Make Your Existing Security Controls More Effective
Sponsored by BitSight
Healthcare Meets Vendor Care
Sponsored by BitSight
Effectively and Efficiently Mitigate Cyber Risk
Sponsored by BitSight
Effective Risk Management With Security Ratings
Sponsored by Kaspersky Lab