Sponsored by Entrust Datacard
Sponsored by Illusive Networks
Harden Your Network Against Silent Attackers Without Impeding Business
Sponsored by Ping Identity
The Power of Identity in Financial Services
Sponsored by Akamai
Increase Business Agility By Adopting Zero Trust
Sponsored by Akamai
5 Steps To Starting Your Cloud Perimeter Journey
Sponsored by Akamai
Remote Access: Security Challenges & Opportunities
Sponsored by Akamai
Five Tough Problems Moving a Traditional Network Security Perimeter to the Cloud
Sponsored by Sift Science
Stopping Content Abuse Before It Happens
Sponsored by Sift Science
The Future of Fraud Fighting
Sponsored by Sift Science
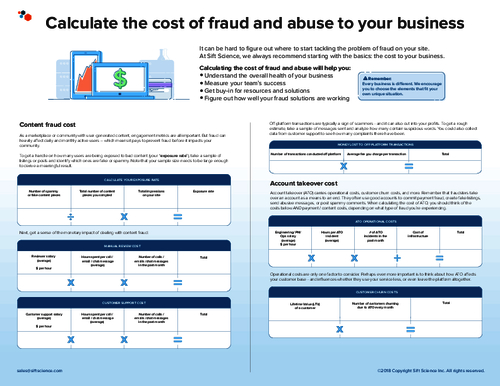
Calculating The Cost of Fraud and Abuse to Your Business
Sponsored by Sift Science
Complete Guide To Preventing Account Takeover
Sponsored by Sift Science
The Retail Industry's Complete Guide To Preventing Account Takeover
Sponsored by Sift Science
E-Commerce's Guide To Stopping Content Abuse Before It Happens
Sponsored by Sift Science
E-Commerce & The Future of Fraud Fighting
Sponsored by IBM