Sponsored by Bomgar
Sponsored by Entrust Datacard
Top 5 Reasons Why Mobile will Transform Enterprise Authentication
Sponsored by Palo Alto Networks
Guidelines for AWS Hybrid Cloud Deployments
Sponsored by Palo Alto Networks
Securely Enabling a Hybrid Cloud in Microsoft Azure
Sponsored by Lastline
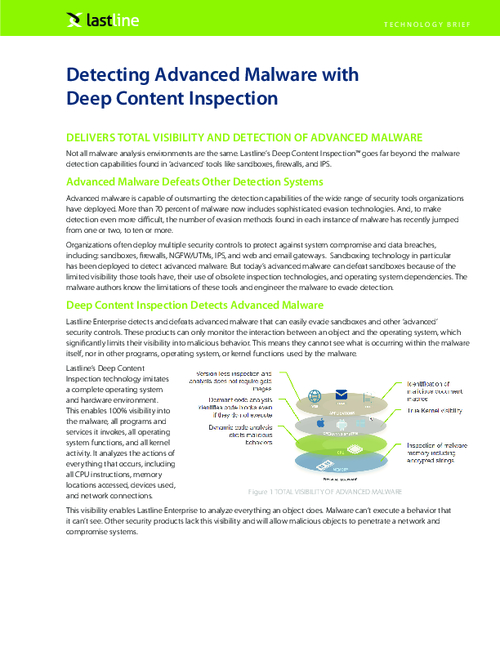
A Breach Detection Rate of 100% wiith Zero False Positives is a Reality
Sponsored by Lastline
The Illusive and Intrusive Advanced Malware; How it Avoids Detection
Sponsored by Harland Clarke
How to Use GRC for PCI DSS Compliance
Sponsored by VMware
The Security Advantages of Micro-Segmentation
Sponsored by VMware
Why Traditional Data Center Security Is No Longer Enough
Sponsored by VMware
Stop Data Center Attacks Before They Happen
Sponsored by VMware
Why Micro-Segmentation Matters Now
Sponsored by Proofpoint
7 Steps to Reduce Social Account Takeover Risk
Sponsored by Proofpoint
Discovering and Reporting Fraudulent Accounts
Sponsored by Lastline
Advanced Malware and How It Avoids Detection
Sponsored by Lastline