Sponsored by IBM
Sponsored by IBM
Preserving the Customer Experience: Survey Results
Sponsored by Check Point Software Technologies
Unknown Malware Continues to Rise
Sponsored by IBM
Mobility Threatscape and New Enterprise Solutions
Sponsored by IBM
The 2017 Mobile Enterprise: Security Challenges
Sponsored by VMware
Get Ready for Windows 10
Sponsored by VMware AirWatch
Five Mobility Trends Making an Impact in the Modern Workplace
Sponsored by VMware AirWatch
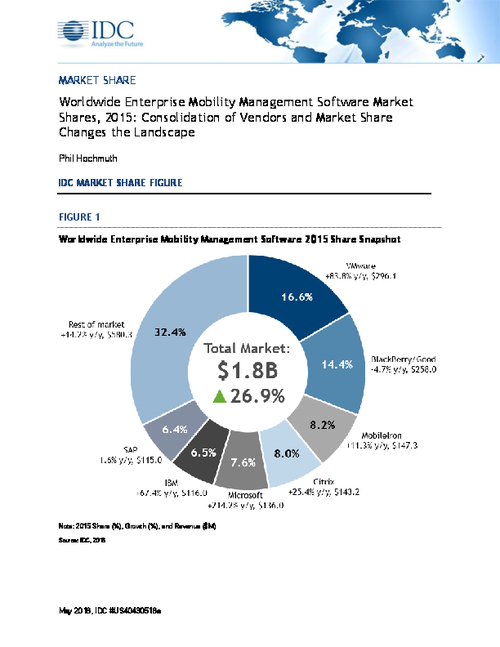
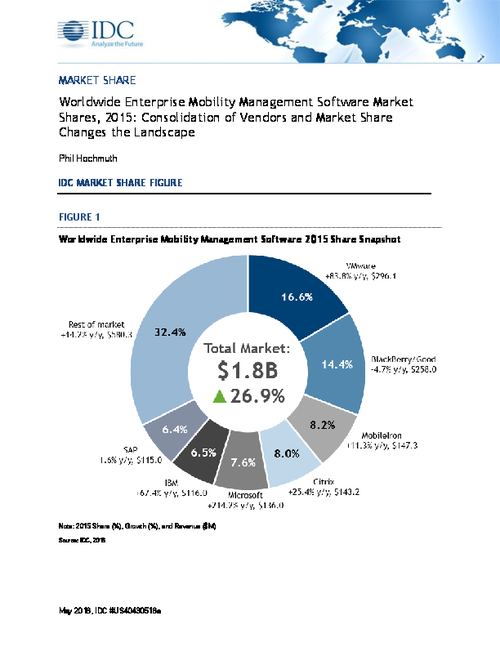
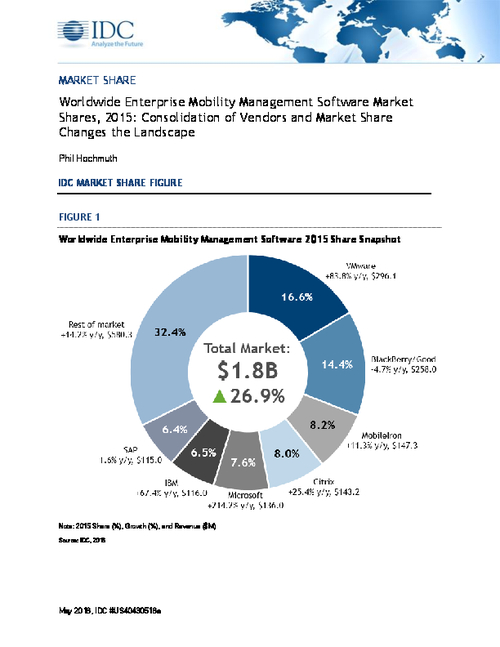
EMM Market Trends by IDC
Sponsored by VMware AirWatch
BYOD Done Right Is a Win Win for Workspace Mobility
Sponsored by VMware AirWatch
The New BYOD: Five Best Practices for a Productive BYOD Program
Sponsored by VMware AirWatch