Sponsored by EdgeWave
Sponsored by EdgeWave
Phishing Thrives During Rising Tide of Cybersecurity Threats
Sponsored by Agari
Securing Office 365: Protect Against Targeted Attacks
Sponsored by Agari
Filling the Security Gaps in Office 365
Sponsored by Agari
The Identity Deception Gap in Office 365
Sponsored by Wombat
2018 Report: Security Awareness Training & Anti-Phishing
Sponsored by Lastline
Office 365 & Gmail Security Measures for SMBs in 2018
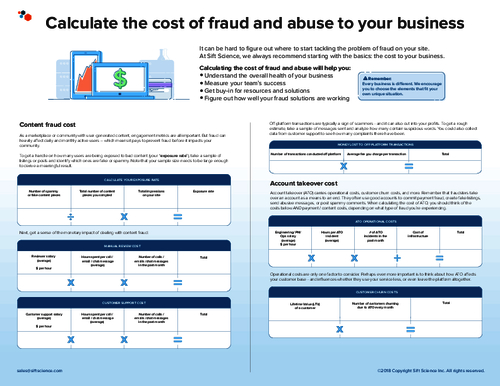
Sponsored by Sift Science
Case Study: Enhancing User Experience While Mitigating Risk
Sponsored by Lastline
A New Look at Email Security: How to Improve Detection of Malicious Payloads
Sponsored by Agari
BEC & ATO: Why Existing Solutions Often Miss the Threats
Sponsored by Wombat
The State of Security Education: Healthcare
Sponsored by Wombat
2018 State of The Phish Report ®
Sponsored by Sift Science
Stopping Content Abuse Before It Happens
Sponsored by Sift Science
The Future of Fraud Fighting
Sponsored by Sift Science