Sponsored by Palo Alto Networks
Sponsored by Lastline
Detecting Advanced Malware with Deep Content Inspection
Sponsored by Lastline
Advanced Malware and How It Avoids Detection
Sponsored by Lastline
Make Your Existing Security Controls More Effective
Sponsored by CrowdStrike
Guide to Antivirus Replacement: What You Need to Know Before Replacing Your Current Solution
Sponsored by LogRhythm
How to Prevent Data Breaches by Reducing Detection and Response Times
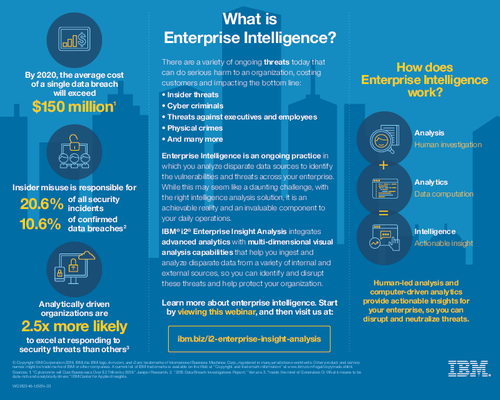
Sponsored by IBM
What is Enterprise Intelligence?
Sponsored by LogRhythm
Seven Ways to Simplify Public Sector Security Intelligence
Sponsored by Tata Communications
The Rise of Security-as-a-Service
Sponsored by Tata Communications
Security-as-a-Service: A Successor to MSS?
Sponsored by Tata Communications
The Evolution of Managed Security Services
Sponsored by IBM
Why Banks Must Protect Customer Endpoints
Sponsored by IBM
Watson for Cyber Security Holds Power and Promise for Security Teams
Sponsored by HelpSystems