Cybercrime , Fraud Management & Cybercrime , Incident & Breach Response
Breach Saga: Bulgarian Tax Agency Fined; Pen Testers Charged
Prosecutors Point to Efforts to Undermine Investigation of Huge Breach
Bulgaria’s Personal Data Protection Commission has fined the country’s National Revenue Agency 5.1 million levs ($2.9 million) for failing to stop a data breach that leaked tax records for nearly all of the country’s adult citizens.
See Also: The Alarming Data Security Vulnerabilities Within Many Enterprises
The fine is the latest action in what has developed into a peculiar criminal case surrounding Bulgaria’s biggest data breach. The National Revenue Agency says the breach exposed data for 5.1 million Bulgarians, including 1.1 million who are deceased. A Bulgarian media outlet reports that the agency plans to appeal the fine.
As a result of an investigation, the Sofia City Prosecutor’s Office has filed criminal charges against three men who worked for a penetration testing company, TAD Group.
Those charged are Ivan Todorov, the founder and CEO of TAD Group; Georgi Yankov, whose LinkedIn profile lists him as a key account manager; and Kristian Boykov, a cybersecurity specialist and penetration tester.
Over the last few weeks, the prosecutor’s office has released pre-trial evidence to underscore its case against the three men. The documents appear to suggest the TAD Group compromised other organizations, perhaps to generate sales leads for its penetration testing consulting business.
Bulgaria is a known for having a somewhat rough-and-tumble business environment, says Vesselin Bontchev, a computer security expert and assistant professor at the Bulgarian Academy of Sciences in Sofia.
Bontchev says he once informed a company that its website was compromised and running a command-and-control server for malware. “When they contacted me, they were surprised that I didn't ask for money,” Bontchev says. “Initially they thought that it was some kind of blackmail scheme.”
TAD Group has offices in Sofia; Newport Beach, California; Atlanta; London; Bucharest; and Dublin. TAD Group officials were not immediately available for comment..
What Data Was Exposed?
The tax office breach occurred in late June and came to light in mid-July. The tax data exposed included national ID numbers, tax and insurance information and VAT [value-added tax] refund information, according to prosecutors. (See: Bulgarian Authorities Arrest Suspect in Massive Data Breach)
The National Revenue Ageny says the exposed data also includes personal data and tax information for foreign individuals and legal entities. For some, it included birth dates, addresses, phone numbers and email addresses. It also includes data on high-level government officials.
The agency says that data belonging to 189 individuals was distributed. It has advised Bulgarian citizens that they do not need to change their identity documents and that the partial data exposed “does not allow for anyone to navigate through your overall assets.”
Boykov was traced by his username. Prosecutor says they found configuration information left on an agency computer, which included a unique username, date, time and information about a software application that was used to read the agency's files.
After Boykov’s arrest, TAD Group issued a statement in Bulgarian defending him. “As part of the company, Christian has always been concerned with ethics, professionalism and loyalty, both to his work commitments, including our clients and the whole team,” the statement says.
Boykov, reached via LinkedIn, tells Information Security Media Group: “Unfortunately, I can't say anything regarding the investigation or the incident."
The prosecutors initially said that they believed Boykov was working alone and not in connection with TAD Group. In the month since, however, that appears to have changed. On Aug. 23, prosecutors announced they were also charging Yankov and Todorov.
Tracing an Email
Sofia prosecutors have released some of the evidence against the three men to bolster their charges in the case and to refute what they claim are efforts to undermine its investigation.
In a strongly worded statement included in an Aug. 23 press release, the prosecutor's office says it's alarming that some individuals, the media and political parties sought to “put their own ambitions above the interests of more than five million Bulgarians. Despite transparency, manipulative allegations are still circulating in the public domain, aiming at the personal abuse of specific magistrates and the overall compromise of the prosecutor’s office.”
The prosecutor's office maintained that it would continue to inform Bulgarian citizens “without endangering the course of criminal proceedings.”
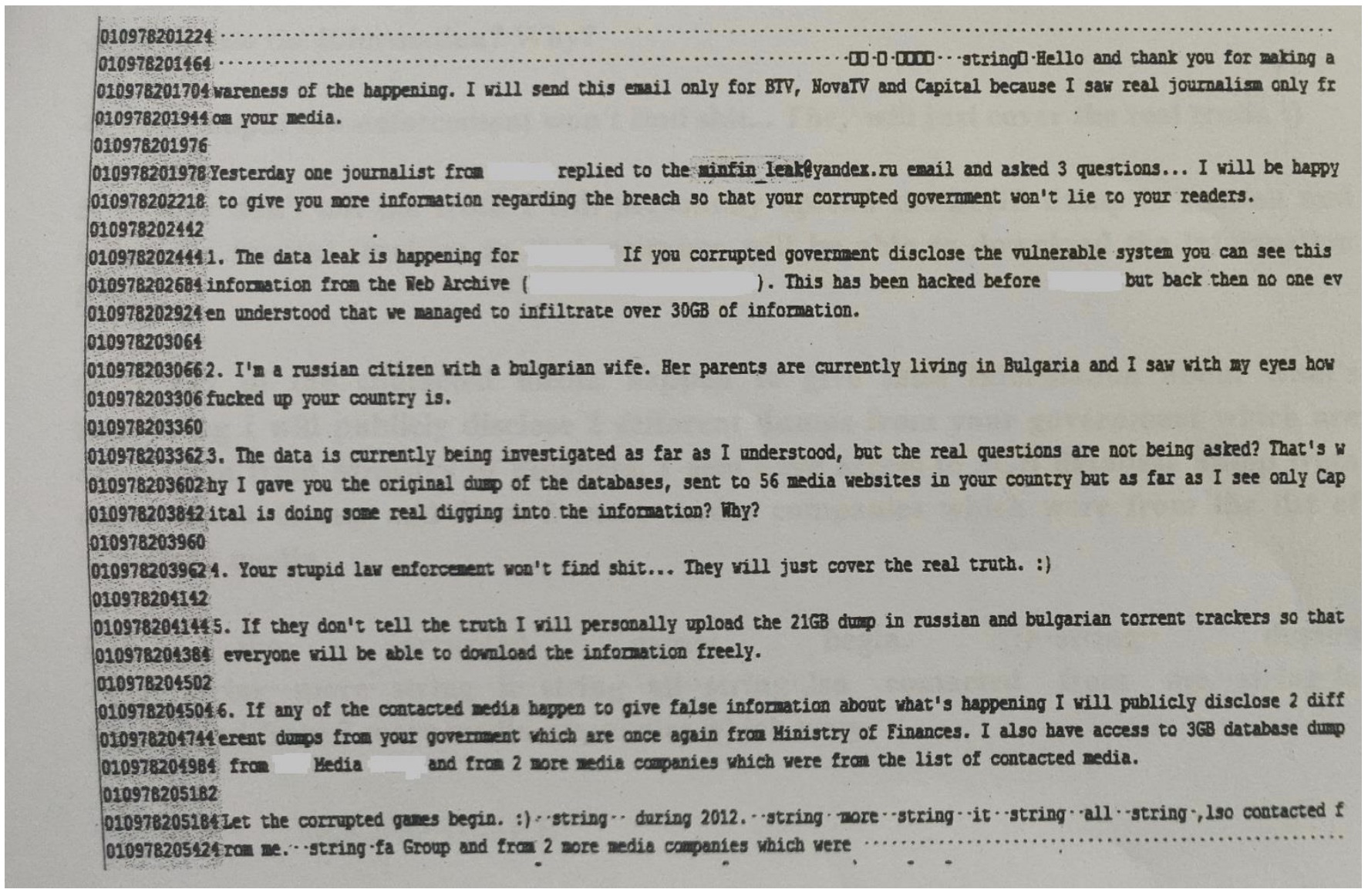
One of the released documents is an email that was allegedly found on the computer of Kristian Boykov. On July 16, three Bulgarian media outlets received an email written in English.
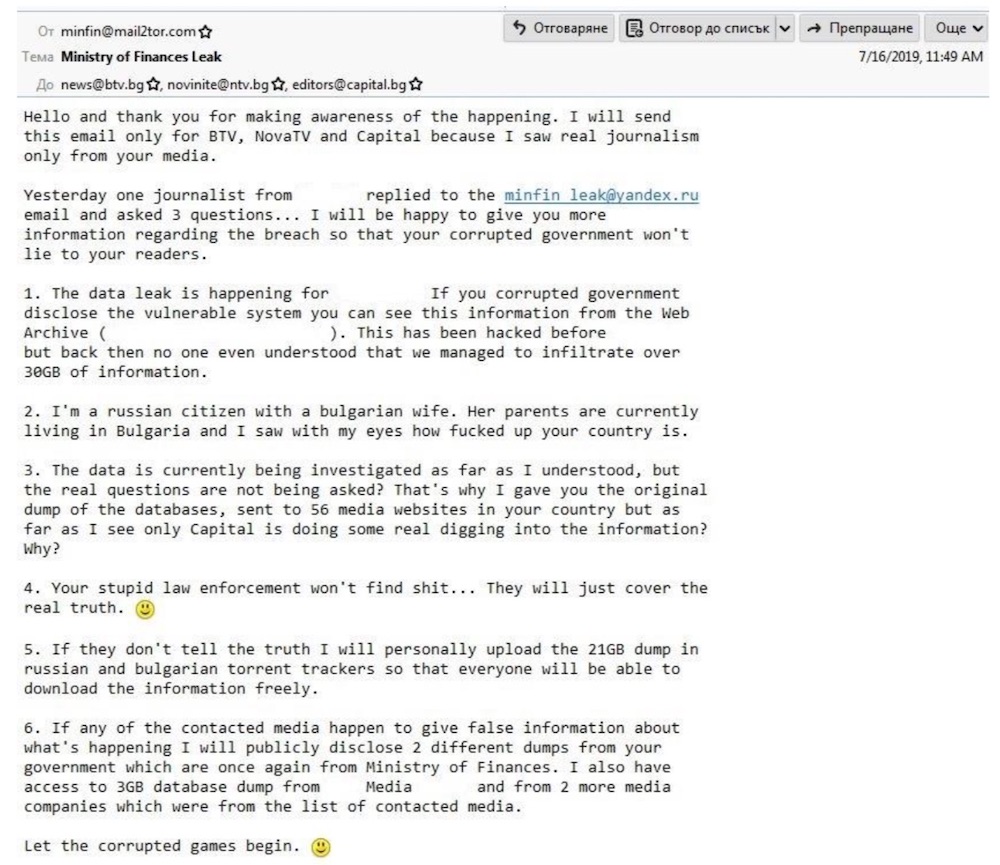
The person who wrote the email identifies himself as a Russian citizen with a Bulgarian wife. He writes that he sent an “original dump” of the National Revenue Agency data to 56 media outlets but only one outlet had paid attention.
The person threatens to “personally upload the 21GB dump in Russian and Bulgarian torrent trackers so that everyone will be able to download the information freely.” He also threatens to dump other information from the Ministry of Finance if the media imparts “false information.”
Prosecutors allege they recovered a deleted email from Boykov’s computer that matched the email received by the three media outlets.
Another document published by the office is a brief transcript of a chat between Yankov and a TAD Group employee identified as “ZM.” The two discussed the arrest of Boykov, which had happened earlier that day, and whether data had been deleted from computers. Prosecutors included a photo of the two men, which was taken from a CCTV camera at TAD Group’s offices.

Witness Statements
Another released document comprises statements taken by the prosecutor’s office from six people, who are only identified by their initials. Their organizations are redacted.
One witness, identified as “RP,” claimed to have been contacted by Todorov by email in July 2018. That witness claims Todorov relayed the presence of a cross-site scripting vulnerability in the organization’s website. The witness claimed the email ended with a proposal for TAD Group’s assistance.
The witness sent an email back to Todorov, refuting TAD Group’s findings. The witness claimed that Todorov confirmed the group’s refutation and offered a “comprehensive security test” without a financial commitment.
Prosecutors published a question-and-answer with another witness, described as “MI,” who is in the insurance industry. MI was presented by prosecutors with a .txt file, which MI identified as data coming from their organization’s systems. But MI says they had no contact with TAD Group.