Sponsored by Palo Alto Networks
Sponsored by Palo Alto Networks
Secure Access Service Edge for Manufacturing
Sponsored by Palo Alto Networks
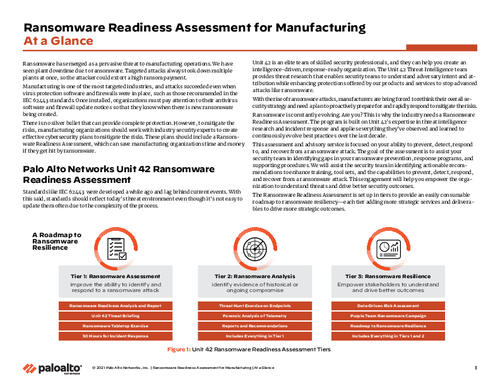
Ransomware Readiness Assessment for Manufacturing At a Glance
Sponsored by Cyberark
Endpoint Least Privilege: A Foundational Security Control
Sponsored by ReliaQuest
Securing The Cloud: How To Increase Cloud Visibility To Power New Business Opportunity
Sponsored by CyberTheory Institute
It’s Time to Implement Maneuver Warfare into your Approach to Cybersecurity
Sponsored by Exabeam
5 Key Things to Achieve in Your First 90 Days as CISO
Sponsored by Exabeam
A CISO’s Guide to Communicating Risk
Sponsored by BioCatch
Spot The Impostor: Tackling the Rise in Social Engineering Scams
Sponsored by Cyberhaven
5 Reasons Why Your DLP Acts like an Outdated Antivirus Product...
Sponsored by CYREBRO
2022 Attack Vector Landscape Analysis
Sponsored by CYREBRO
How to Build a SOC: A Complete Guide
Sponsored by Cyberhaven